The lawful access debate in Canada has to date focused on privacy concerns such as access to subscriber information, mandatory metadata retention, and international production orders. But there is another dimension to Bill C-22 that has received less attention and may matter even more to the daily security of Canadians: the risk that the bill’s surveillance-capability requirements and lack of clarity about systemic vulnerabilities will make Canadians less secure. The international experience with similar laws is not reassuring, as it points to risks of hacking, removal of security features that protect users, and reduced investment and innovation. Bill C-22 heads in much the same direction.
The relevant provisions are in the second half of Bill C-22, the Supporting Authorized Access to Information Act. As discussed on the Law Bytes roundtable podcast on lawful access, the SAAIA envisions a wide range of obligations for providers, including “developing, implementing, assessing, testing, and maintaining operational and technical capabilities to extract and organize information authorized for access.” It also covers installing and maintaining devices that enable authorized persons to access that information, as well as retaining metadata for up to a year. The scope of these obligations should not be understated, as they mandate broad access to encrypted devices and services as well as envision the incorporation of surveillance technologies into their systems.
The bill identifies two types of providers that may be subject to these obligations: electronic service providers and core providers. Electronic service providers cover any service provider that offers electronic services that involve the “creation, recording, storage, processing, transmission, reception, emission or making available of information in electronic, digital or any other intangible form by an electronic, digital, magnetic, optical, biometric, acoustic or other technological means.” In other words, it covers just about anyone offering a service in electronic or digital form. Core providers are a subset of electronic service providers. The bill doesn’t say much about who will be designated as core providers, other than that this will be determined by government regulation and core providers will be listed in a schedule to the Act.
Core providers face the most significant obligations, including those mentioned above. Those that fall outside of the core provider regulation – ie, the remaining electronic service providers – are required to provide “all reasonable assistance” to permit the assessment or testing of any device or equipment that may enable an authorized person to access information. Moreover, Section 7 of the bill gives the Minister the power to issue an order to electronic service providers that imposes the same obligations as those imposed on core providers (subject to the electronic service provider being permitted to make representations to the Minister and approval by the Intelligence Commissioner). The extensive obligations will therefore be applied to all core providers and could be extended to any electronic service provider.
The bill includes a safeguard which states that a provider is not required to comply with a regulation if compliance would require it “to introduce a systemic vulnerability related to that service or prevent the provider from rectifying such a vulnerability.” The problem is that the term “systemic vulnerability” is vaguely defined as a “vulnerability in the electronic protections of an electronic service that creates a substantial risk that secure information could be accessed by a person who does not have any right or authority to do so.” There is a further definition for “electronic protections” that includes authentication, encryption and any other prescribed type of data protection. There are no specifics on what any of this means, and the entire framework is ultimately subject to a future regulation-making process. Moreover, all of this, including any Ministerial orders, must be kept secret from the public.
In fact, the safeguard may be in direct tension with the bill’s own enforcement framework. Sections 5(5) and 7(5) state that a provider “is not required to comply” if compliance would create a systemic vulnerability. But Section 12 provides that an electronic service provider “that is subject to an order made under subsection 7(1) must comply with it” and Section 13 specifies that orders take primacy over regulations when there are inconsistencies. This creates a structural contradiction: the safeguard says you do not have to comply, but the enforcement provisions say you must. The bill offers no clear mechanism to resolve this conflict and no accessible process for providers to challenge an order they believe would compromise their systems’ security.
The bill, therefore, raises serious concerns, which are exacerbated by international experiences with similar provisions. In the United States, CALEA, which was enacted in 1994, requires telecommunications carriers to ensure that their equipment, facilities, and services are capable of “expeditiously isolating and enabling the government, pursuant to a court order or other lawful authorization, to intercept … all wire and electronic communications carried by the carrier.” In other words, every telecom must build wiretapping capability into its network. CALEA contains a narrow carve-out for encryption, which exempts the carrier from being responsible for decrypting communications encrypted by a subscriber, unless the carrier provided the encryption and possesses the decryption key. But it contains no systemic vulnerability exception, nor a provision that allows a carrier to refuse to comply if doing so would compromise the security of its network.
In late 2024, the consequences of that omission became clear. Chinese state-sponsored hackers known as Salt Typhoon exploited lawful intercept infrastructure that U.S. telecoms were required to maintain, gaining access to wiretap systems at nine major carriers, including AT&T, Verizon, and T-Mobile. They used that access to obtain metadata from over a million users, real-time recordings of phone calls involving senior political figures, and nearly complete lists of phone numbers under active law enforcement surveillance. The Bill C-22 core provider obligations under s. 5(2)(a) and (b), which require the development of interception capabilities and the installation of devices enabling authorized access, are functionally the Canadian equivalent of CALEA’s capability requirements.
The UK’s Investigatory Powers Act 2016 takes a different approach. Section 253 empowers the Home Secretary to issue a “technical capability notice” requiring a telecommunications operator to maintain the capability to assist with interception warrants, equipment interference warrants, and communications data authorizations. The statutory language refers to “electronic protection” rather than encryption specifically, but the effect is the same: the government can require a company to undo its own security measures. Critically, the IPA contains no exception for systemic vulnerability.
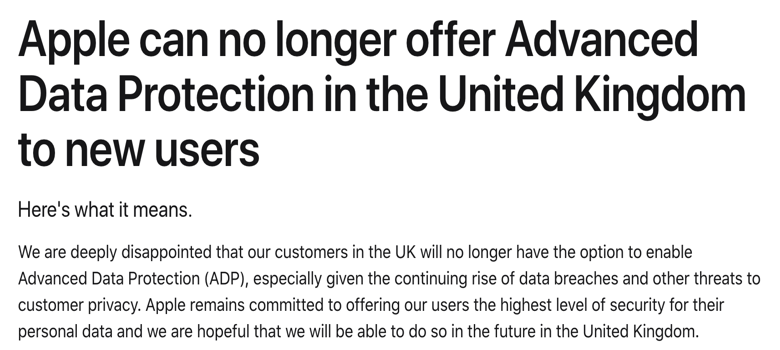
In January 2025, the UK Home Office issued Apple a secret technical capability notice demanding that Apple provide the capability to access all iCloud data for any user worldwide, regardless of whether that data is protected by Apple’s end-to-end encryption feature, Advanced Data Protection. Apple refused to build a backdoor and instead withdrew the service from the UK entirely. Apple launched a legal challenge, and the UK eventually backed down on the global demand. However, reports suggest it continued to seek access to UK users’ encrypted data through a second notice. Bill C-22’s systemic vulnerability exception is designed to avoid this outcome, but the exception only works if it is defined clearly enough to prevent the same dynamic from playing out in practice.
Australia’s Telecommunications and Other Legislation Amendment (Assistance and Access) Act 2018 features voluntary technical assistance requests, compulsory technical assistance notices, and technical capability notices that can require providers to build new capabilities. The Australian approach includes a systemic vulnerability exception, which is defined in the statute. But even with these statutory definitions, the Australian experience has not been reassuring. The Australian Information Commissioner and Privacy Commissioner repeatedly recommended further clarification, noting that terms like “whole class of technology,” “target technologies,” and “connected” remain ambiguous. Apple warned that the law could allow the government to order smart home speakers to install eavesdropping capabilities or require the development of a tool to unlock a user’s device, regardless of whether it could unlock every other user’s device. Perhaps most revealing is that the law has been almost entirely unused: as of late 2024, no technical capability notice had been publicly reported as having been used.
The lesson from all three jurisdictions is the same, namely that mandating surveillance capabilities creates security risks. Bill C-22’s systemic vulnerability exception acknowledges that the risk is real. But a poorly defined exception subject to unknown regulations is not an effective safeguard. This aspect of the bill requires a significant overhaul that includes detailed definitions in the statute (not future regulations), mandatory, independent technical assessments before any capability requirements are imposed, a sunset clause to reassess the impact of the new rules, clarity on the inconsistencies with regard to compliance requirements, and the right to seek judicial review in the event of a risk of compromised security. Failure to address these issues in Bill C-22 places Canadians’ privacy and security at risk.
Enjoyed this post? Get every post plus the Law Bytes podcast delivered to your inbox – subscribe on Substack.