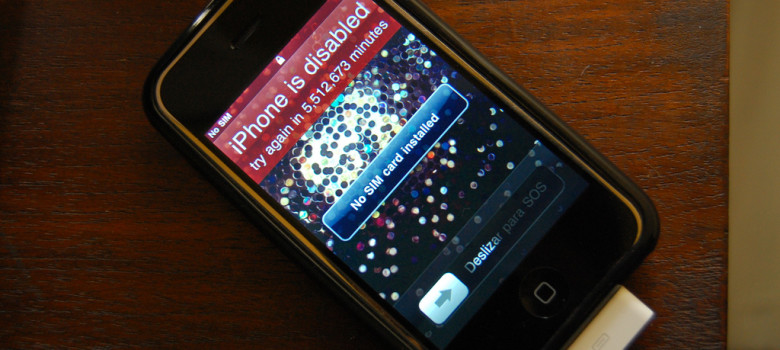
The news that the U.S. government has obtained a court order requiring Apple to assist law enforcement to break the encryption on an iPhone owned by one of the San Bernadino terrorists has sparked widespread concern. There is some debate over the scope of the judicial order – Techdirt points out that the order does not require Apple to break its encryption but rather allow the government to “brute force” the password without deleting the data – but it is clear that the goal is to limit the effectiveness of the encryption protections found on the popular device. Apple has issued a public letter stating its view that this is a dangerous precedent that could be repeated over and over again. Indeed, if a U.S. court can issue such an order, there is seemingly nothing to stop other governments from doing the same.
What does this have to do with the TPP?
The U.S. has suggested that the TPP would address these issues, claiming that the agreement:
Ensures that companies and individuals are able to use the cybersecurity and encryption tools they see fit, without arbitrary restrictions that could stifle free expression.
The Trouble with the TPP is that a closer examination of the deal reveals that it would not stop any member country from issuing an order similar to the U.S. one involving Apple. The U.S. claims involving encryption tools stem from Chapter 8 on Technical Barriers to Trade. Annex 8-B, Section A deals with cryptography:
With respect to a product that uses cryptography and is designed for commercial applications, no Party may impose or maintain a technical regulation or conformity assessment procedure that requires a manufacturer or supplier of the product, as a condition of the manufacture, sale, distribution, import or use of the product, to:
(a) transfer or provide access to a particular technology, production process, or other information (such as a private key or other secret parameter, algorithm specification or other design detail), that is proprietary to the manufacturer or supplier and relates to the cryptography in the product, to the Party or a person in the Party’s territory;
(b) partner with a person in its territory; or
(c) use or integrate a particular cryptographic algorithm or cipher, other than where the manufacture, sale, distribution, import or use of the product is by or for the government of the Party.
Taken on its own, this provision creates some limitations on legislated encryption backdoors. Yet as with many aspects of the TPP, the devil is in the details. This provision is quickly followed with this exception:
For greater certainty, nothing in this Section shall be construed to prevent law enforcement authorities from requiring service suppliers using encryption they control from providing, pursuant to legal procedures, unencrypted communications.
In other words, the TPP may permit the kind of order issued yesterday. In fact, the EFF points out that the TPP goes further, with several other loopholes and exceptions. It characterizes the end result in the following way:
So what appears on the surface to be strong protection for crypto software in the TPP is actually much weaker than it seems: it doesn’t prevent the government from requiring providers to give them access to decrypted data, it doesn’t protect developers against backdoor demands from their own government, it doesn’t protect tools from countries that aren’t TPP signatories, it doesn’t stop a country from demanding access to private keys of a product so long as this demand is not a condition of supply of that product within the country, and on top of all that, there is a sweeping national security exception that can override the provision altogether.
Apple has committed to fighting the judicial order. It might consider doing the same with the TPP.
(prior posts in the series include Day 1: US Blocks Balancing Provisions, Day 2: Locking in Digital Locks, Day 3: Copyright Term Extension, Day 4: Copyright Notice and Takedown Rules, Day 5: Rights Holders “Shall” vs. Users “May”, Day 6: Price of Entry, Day 7: Patent Term Extensions, Day 8: Locking in Biologics Protection, Day 9: Limits on Medical Devices and Pharma Data Collection, Day 10: Criminalization of Trade Secret Law, Day 11: Weak Privacy Standards, Day 12: Restrictions on Data Localization Requirements, Day 13: Ban on Data Transfer Restrictions, Day 14: No U.S. Assurances for Canada on Privacy, Day 15: Weak Anti-Spam Law Standards, Day 16: Intervening in Internet Governance, Day 17: Weak E-commerce Rules, Day 18: Failure to Protect Canadian Cultural Policy, Day 19: No Canadian Side Agreement to Advance Tech Sector, Day 20: Unenforceable Net Neutrality Rules, Day 21: U.S. Requires Canadian Anti-Counterfeiting Report Card, Day 22: Expanding Border Measures Without Court Oversight, Day 23: On Signing Day, What Comes Next?, Day 24: Missing Balance on IP Border Measures, Day 25: The Treaties With the Treaty, Day 26: Why It Limits Canadian Cultural Policies, Day 27: Source Code Disclosure Confusion, Day 28: Privacy Risks from Source Code Rules, Day 29: Cultural Policy Innovation Uncertainty, Day 30: Losing Our Way on Geographical Indications, Day 31: Canadian Trademark Law Overhaul)







Missing from the discussion of Apple is the fact that Apple has access to the unencrypted information through their own back doors, and this is only a discussion of whether the government should have access to it as well. Real security can only come when devices are locked by their owners, not the manufacturers, and that laws are put in place to protect the owners (and ill advised laws which protect manufacturers from owners repealed).
Given the TPP ratchets up the anti-circumvention (IE: anti-ownership) provisions, this is the far greater security threat than worrying about what governments have legal access to.
“…Apple has access to the unencrypted information through their own back doors…”
I’m not sure where you got that. It doesn’t sound logical.
When you use end-to-end encryption, there should be no unencrypted anything in the provider’s domain to have access to.
That is supposed to be part of Apple’s argument. Since Apple has no access to this particular information, the only option was to break into the phones themselves for their decrypted content.
Since the phone destroys the content after 10 wrong attempts, Apple is being asked to create a malware to circumvent that, and another security feature, in order to break the passwords.
Cook clearly understands the implications of doing such a thing, and is rightly challenging the order.
I personally agree with this stance, as:
1) there are no assurances that this “tool” will not be widely abused, once it’s created, and every indication it will be., and
2) Apple should not have to circumvent its own product, along with any public trust in that product.
The section of the TPP indicates “using encryption they control”, meaning that the provision only applies to service providers like Apple which have control over the devices rather than the owners. It would not require a hardware manufacturer to disallow owners from installing their own privacy enhancing operating systems — that is Apple that is denying owners that, not the TPP.
You are making an argument about encryption, and one that would apply to RIM (Where they had apps that, because they weren’t using end-to-end encryption but apps which communicated with their servers and only protected against third parties and not RIM itself). In this case the problem is that Apple controls one of the ends (the Apple manufactured hardware with Apple locked software), and thus has access to unencrypted data which governments can force them to provide.
While the TPP provisions are obviously troubling, the real problem here has been the opposition to owners rights inherent in Apples’ business model. The concept of “jail breaking” only exists because owners have had to fight Apple and laws they have pushed forward (anti-circumvention, etc) for basic owners rights.
I don’t disagree with the owner’s rights concerns. And, this is no way in defense of any of Apple’s other bizarre behaviours.
But, you’re still not making sense about Apple’s “access to unencrypted data”. They may control the hardware in the users’ hands to a large degree, but that doesn’t give them access to any of the pertinent content the government might want to force from their hands.
If it weren’t for that fact, the government would be pressing for that available, unencrypted content, rather than trying to force Apple to circumvent the product itself.
That user-generated content is what is locked away by the encryption. That is Apple’s point.
My point is this: in order for files to be stored and accessed by the user of a device the keys must exist on the device to encrypt/decrypt. The software on that device (which is what Apple controls) then has access to the keys and the unencrypted data.
Even the argument that you need to type in a PIN to get access to the keys is moot because Apple software is what you are typing that PIN into, and they can be legally compelled to keep a copy of it. Some might claim that is a “back door”, but so is the entire legal theory behind anti-circumvention laws which Apple has been instrumental in putting in place.
This is not a network file storage device or cloud service that Apple is providing, where data can be encrypted before it is sent to the device/provider for storage and those who control the software on the device don’t have access to the unencrypted data. This is Apple having complete control over the device that is doing the encryption, and thus has access to the unencrypted data and keys.
People aren’t encrypting data in their heads and then typing hex codes into the touch-keyboard. That would be the only way that ‘end-to-end’ encryption would avoid Apple having access to the unencrypted data.
Apple can’t have it both ways: either they can claim to Hollywood that they have “secured iPhones against control by their owners” or they can claim to police forces that they have “not secured iPhones against control by their owners”.
This is an example of a bad case giving us bad caselaw. Because Apple has always been opposed to owners rights they may cause precedent to be set that will make it even harder for owners to be legally allowed to control their own hardware. Thin edge of the wedge will be laws that force the companies who control the devices (IE: Apple) to grant lawful access, and next it will be governments declaring CyanogenMod illegal because there is no manufacturer to go after to get lawful access.
As to “circumventing the product itself”, there is a lot of mixed messages coming from the media and press releases from various companies. I take anything that has its origins from Apple with a grain of salt. What I’ve seen reported is the government demanding access to the fruits of the type of third-party control which Apple has been lobbying for for decades, and there has been no greater request from the government to “back-door” devices than Apple already demanded with anti-circumvention legislation.
…Except, Apple DOESN’T have the keys you’re formulating your entire premise around.
They would literally have to extract hardware chips from the phone in question, and execute a few invasive procedures, in order to obtain the keys being used.
Despite all the other anti-user processes, this is the one good thing that Apple did. Not only did it favour the user (for a change), it should have provided Apple a relief from the snowballing trend of law enforcement requests.
“…Except, Apple DOESN’T have the keys you’re formulating your entire premise around.”
Did you read the relevant source code to come to that conclusion, or are you basing that on Apple press releases? Whether they claim otherwise, they do control the software which has access to those keys. If Apple has claimed they have chosen not to keep copies of keys themselves that is simply a claim, not something that can be proven without access to the source code and verification that the software running on the device matches the source code. Allowing third party audits of software is something that Apple has denied, and has pushed for anti-circumvention laws to make unlawful.
This is the nature of the dilemma that Apple have put themselves in. By wanting control over what software is installed on someone elses hardware they have put themselves in the path for agencies wanting lawful access to the devices. Even if they aren’t keeping access to the keys they claim they aren’t, that won’t absolve them from responsibility of supplying them to law enforcement considering they do control the software which controls the keys.
Apple have also put themselves in the middle of a political fight, where some commenter can quite legitimately suggest Apple stands in the way of public safety and national security. Given the well-known harm to computer security that comes from the anti-circumvention laws they have promoted I have always believed this to be the case, but now people who might have otherwise sided with Apple will be opposed.
Disclaimers:
1) You couldn’t pay me to believe ANYONE’S press release,
2) I’ve been part of the tech world for a good number of years. (I do read source code, and I know my way around many products quite well.)
3) I’m no Apple fanboy, that’s for sure. I’ve always chosen to never buy Apple products for my own use. (I was, however, recently given an iPad, which I’m currently setting up to operate outside of the Apple bubble.)
I know what you’re trying to say, but trust me, it’s wrong. (No disrespect.)
A) The software on the device doesn’t “access” encryption keys. Hardware components contain keys embedded in their chips, and apply the encryption.
All the software can do is create the content and call for the transmission. Even if you could “view” the keys from inside the software, you’d have to be logged in as the authorized user (which takes us to the place we are now).
B) The keys are not in Apple’s “possession”. They are embedded in the device hardware. It would be a conundrum for Apple to have record of all the pertinent keys, and a legal nightmare if they did.
The embedded hardware approach was certainly their attempt to avoid all that, and I think it was actually the right thing to do for everyone’s sake.
C) This is actually not a case that illustrates Apple’s “control” policies. It’s actually something they got right for a change. The users wanted better security, and they actually listened and delivered that.
I know you’ve got issues with Apple. So do I.
But, I have a bigger problem with the way government, law enforcement, and related “authorities” are presently walking all over everyone’s rights, supposedly to fight an enemy that apparently only the government sees.
EFF Reports:
Sneaky Change to the TPP Drastically Extends Criminal Penalties
https://www.eff.org/deeplinks/2016/02/sneaky-change-tpp-drastically-extends-criminal-penalties
What does this surreptitious change from “paragraph” to “subparagraph” mean? Well, in its original form the provision exempted a country from making available any of the criminal procedures and penalties listed above, except in circumstances where there was an impact on the copyright holder’s ability to exploit their work in the market.
In its revised form, the only criminal provision that a country is exempted from applying in those circumstances is the one to which the footnote is attached—namely, the ex officio action provision. Which means, under this amendment, all of the other criminal procedures and penalties must be available even if the infringement has absolutely no impact on the right holder’s ability to exploit their work in the market. The only enforcement provision that countries have the flexibility to withhold in such cases is the authority of state officials to take legal action into their own hands.
Sneaky, huh?
phones! (gave them up in 80 when I didn’t like telus response to a frenzied market in calgary’s first oil boom. Haven’t looked back; other monpolies are behaving much the same way now.)
poisonous, expensive, leaky.
is it mandatory yet? everything else forbidden illegal, and culpable?
(ALL your traffic belongsg to us, including whatever we dump on you. Beware, most of it is illegal.)
worse yet, you’re not even paid for it. That’s why i don;t watch TV, and gave that up.
except for the weather station, I do have to admit.